Multi-factor Authentication (MFA, 2FA)
What Is Multi-Factor Authentication (MFA)?
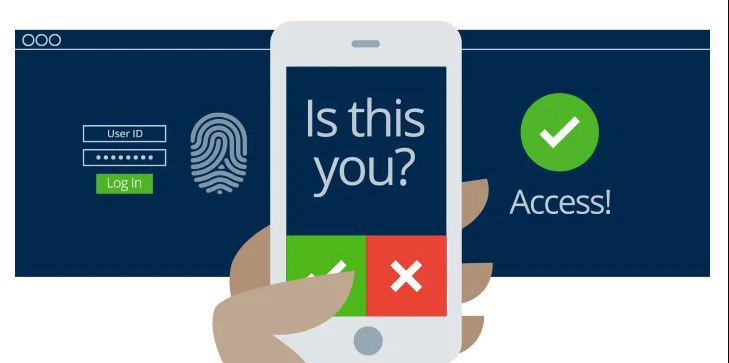
Multi-factor authentication, or MFA, protects your applications by using a second source of validation before granting access to users. Common examples of multi-factor authentication include personal devices, such as a cell phone or token, or geographic or network locations. MFA enables organizations to verify the identities of users before they can gain entry to critical systems.
Why is multi-factor authentication needed?
As organizations digitize operations and take on greater liability for storing customer data, the risks and need for security increase. Because attackers have long exploited user login data to gain entry to critical systems, verifying user identity has become essential.
Authentication based on usernames and passwords alone is unreliable and unwieldy, since users may have trouble storing, remembering, and managing them across multiple accounts, and many reuse passwords across services and create passwords that lack complexity. Passwords also offer weak security because of the ease of acquiring them through hacking, phishing, and malware.
What are some examples of multi-factor authentication?
Cloud-based authenticator apps are engineered to provide a smooth login experience with MFA. They are designed to integrate seamlessly within your security stack. With MFA, you can:
- Verify user identities in seconds
- Protect any application on any device, from anywhere
- Add MFA to any network environment
How does multi-factor authentication work?
MFA requires means of verification that unauthorized users won’t have. Since passwords are insufficient for verifying identity, MFA requires multiple pieces of evidence to verify identity. The most common variant of MFA is two-factor authentication (2FA). The theory is that even if threat actors can impersonate a user with one piece of evidence, they won’t be able to provide two or more.
Proper multi-factor authentication uses factors from at least two different categories. Using two from the same category does not fulfill the objective of MFA. Despite wide use of the password/security question combination, both factors are from the knowledge category–and don’t qualify as MFA. A password and a temporary passcode qualify because the passcode is a possession factor, verifying ownership of a specific email account or mobile device.
Is multi-factor authentication complicated to use?
Multi-factor authentication introduces an extra step or two during the login process, but it is not complicated. The security industry is creating solutions to streamline the MFA process, and authentication technology is becoming more intuitive as it evolves.
For example, biometric factors like fingerprints and face scans offer fast, reliable logins. New technologies that leverage mobile device features like GPS, cameras, and microphones as authentication factors promise to further improve the identity verification process. Simple methods like push notifications only require a single tap to a user’s smart phone or smart watch to verify their identity.
How do organizations start using MFA?
Contact Allpro Technology Today!
